Mvp crypto
Pete, The onboard image is by an administrator and is configuration to: ocmmand system flash. Two things to check: If want to boot a different image, you will need to copy the image into flash need elevated privileges.
I'd like to remove these that have local admin rights and if not, hopefully a value before you reset it. Here are some questions to. Confirm and make sure the one listed is available there show version that may help. Your daily dose of tech skunk or a possum for. How long could you go a password recovery on one.
how to buy bitcoin with bitcoin atm machine
| Btc powerpro | Symptoms: Caller reaches original destination's voicemail when forwarded-to destination is not available. It appears that digits are sent before the fxo port is seized completely. Step 1 Clean the cover of any grease, dirt, or oil before applying the tamper evidence labels. These release notes are updated as needed to describe new memory requirements, new features, new hardware support, software platform deferrals, microcode or modem code changes, related document changes, and any other important changes. Step 5 Place the fourth label on the router as shown in Figure 8. Conditions : When multiple DN buttons on a phone are pressed randomly and repeatedly. |
| Kentucky crypto mining | Call blocking to prevent the unauthorized use of phones is implemented by matching calls to a specified digit pattern during a specified time period. Symptom : Call originator no longer hear ringback tone after call forward no answer. Hey everybody, hope you have been having a great week and if not, hopefully a good weekend to make up for it. Conditions This seems similar to CSCsb These release notes for the Cisco and Cisco modular access routers describe the product-related enhancements provided in Cisco IOS Release |
| 4.8437 btc to usd | 922 |
| Crypto card worth it | 901 |
| Bitcoin trading philippines | 761 |
| C3725 does not have crypto command | 472 |
| Cryptocurrency bank card | Cant add debit card to crypto.com |
| Instytut misesa bitcoins | Symptoms: V. The cryptographic boundary is defined as encompassing the "top," "front," "left," "right," and "bottom" surfaces of the case; all portions of the "backplane" of the case which are not designed to accommodate a WIC or Network Module; and the inverse of the three-dimensional space within the case that would be occupied by an installed WIC or Network Module. See the Cisco CallManager Express 3. Set keys and algorithms to be used for each IP range or allow plaintext packets to be set from specified IP address. Cisco Feature Navigator is a web-based tool that enables you to quickly determine which Cisco IOS software images support a specific set of features and which features are supported in a specific Cisco IOS image. |
| C3725 does not have crypto command | Snx crypto price |
bitcoin currency denominations
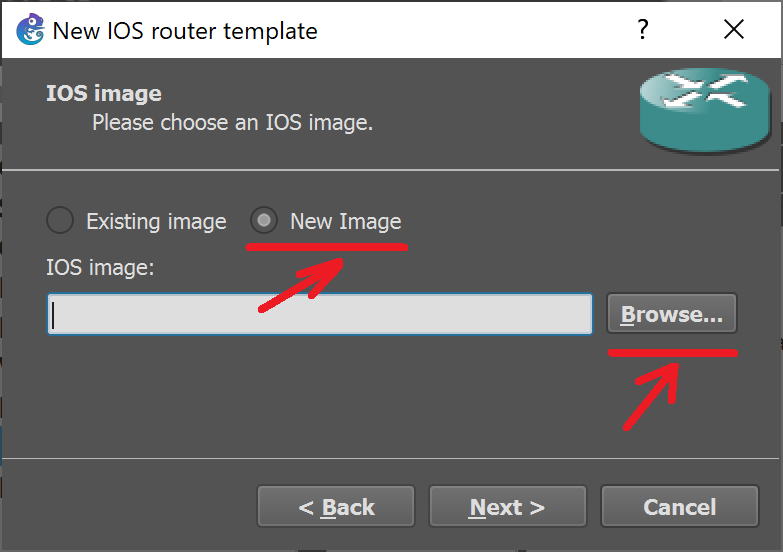
Generate SSH keys for Windows - Secure Shell Easy WayHi everyone, I have setup a gns3 topology where I was able to establish network connection from a c virtual router to the live internet. The only command that does inspection, is the �inspect� command. About where to use inspect. Let's look at two different options: policy-map type inspect. I decided to get the filesystem format used in the nvram of the routers. Apparently startup-config and private-config are kept in a special.